Timeline
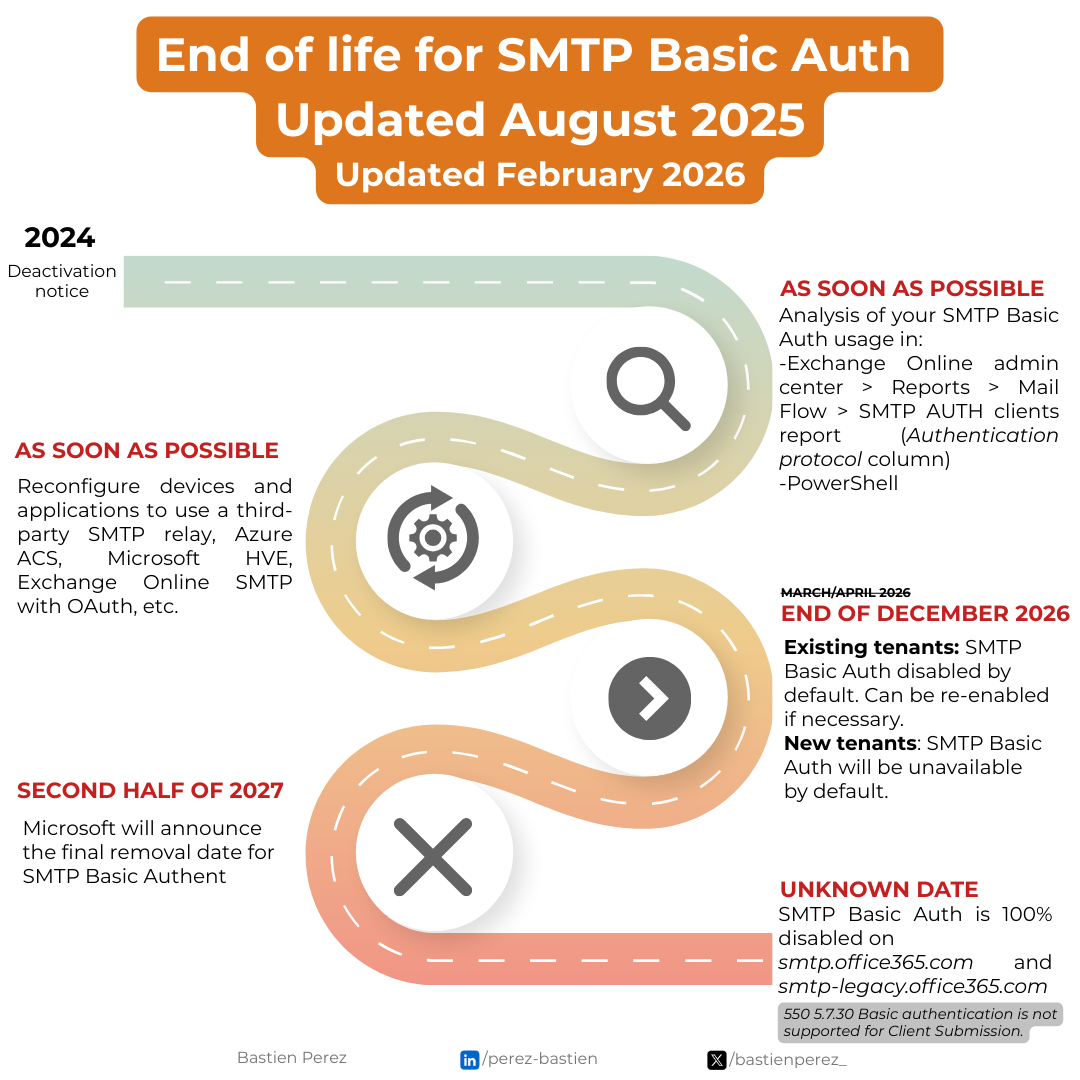
The end of basic authentication on SMTP (SMTP Basic Auth) in Exchange Online has been postponed again. Initially scheduled for September 2025, then April 2026, the official date for the total and definitive removal of SMTP Basic Auth is currently unknown, but we do have new deadlines. In January 2027, Microsoft updated its schedule:
- Now to December 2026: SMTP AUTH Basic Authentication behavior remains unchanged.
- End of December 2026:
- Existing tenants : SMTP AUTH Basic Authentication will be disabled by default. Administrators will still be able to enable it if needed.
- New tenants created after December 2026: SMTP AUTH Basic Authentication will be unavailable by default. OAuth will be the supported authentication method.
- Second half of 2027: Microsoft will announce the final removal date for SMTP AUTH Basic Authentication.
The new deadlines are shown in the image below.
SMTP Auth Report
Get a summary report of SMTP Auth
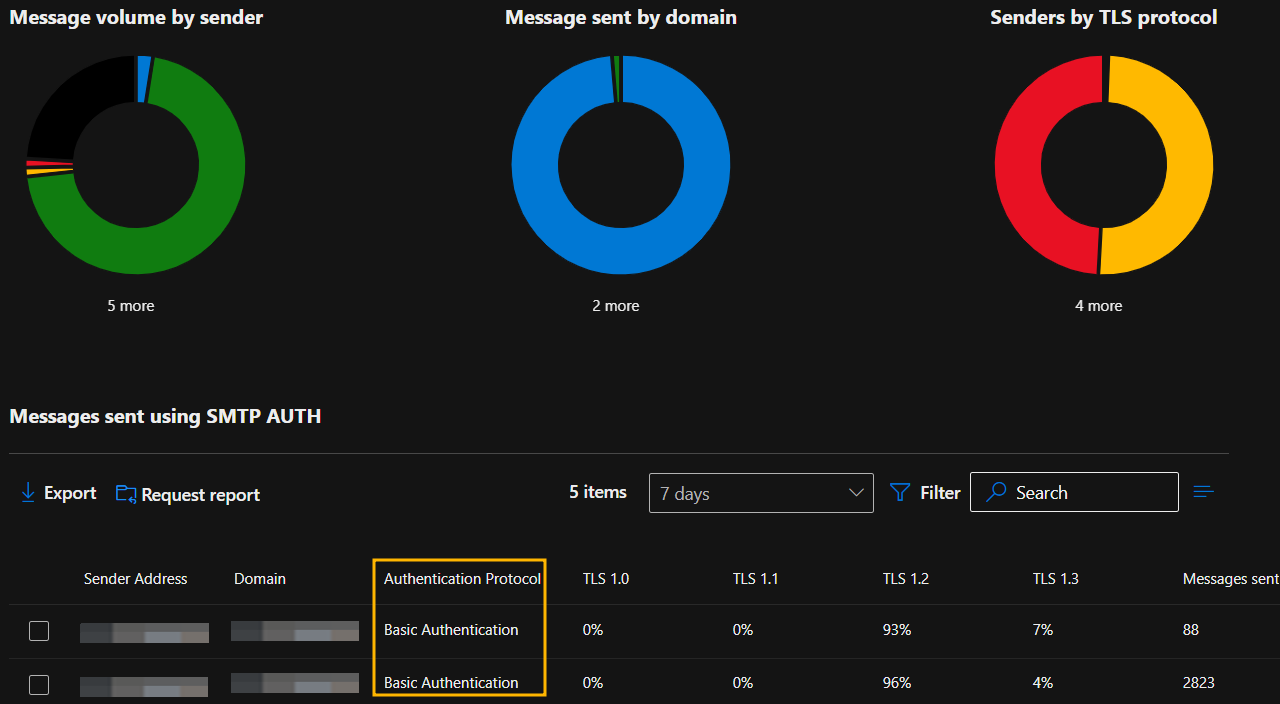
To identify accounts or addresses using Basic SMTP Authentication, Microsoft provides reports.
Go to Exchange Online Admin Center > Reports > Mail Flow> SMTP AUTH clients report (Direct link: https://admin.cloud.microsoft/exchange?#/reports/smtpauthmailflowdetails)
In the report, check the Authentication protocol column and look for the value Basic Authentication to identify accounts that use this.
Get detailled SMTP Auth Report via Exchange Admin Center
If you want more details about the specific emails, you can request a full report by clicking on Request Report.
This report contains:
datemessage_idsenderNamesenderDomaintls_versiontls_cipheroriginal_client_ip: By default, reports in the Exchange Admin Center display "PII" (Personally Identifiable Information) instead of the actual IP address. To show the real values, go to https://admin.cloud.microsoft/#/Settings/Services/:/Settings/L1/Reports and checkDisplay concealed user, group, and site names in all reports. Ensure this setting complies with your company’s confidentiality policy before applying it.authMethod: Values are eitherTlsAuthLogin(Basic Authentication) orXOAUTH2(Modern Authentication). Pay close attention to TlsAuthLogin, as it corresponds to Basic Authentication that must be stopped.message_count
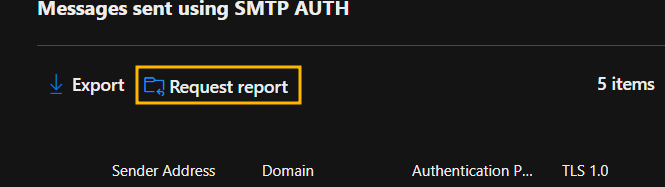
You’ll need to enter a name, a start and end date, and an email address to receive the download link. Depending on your email volume, report generation may take several hours.
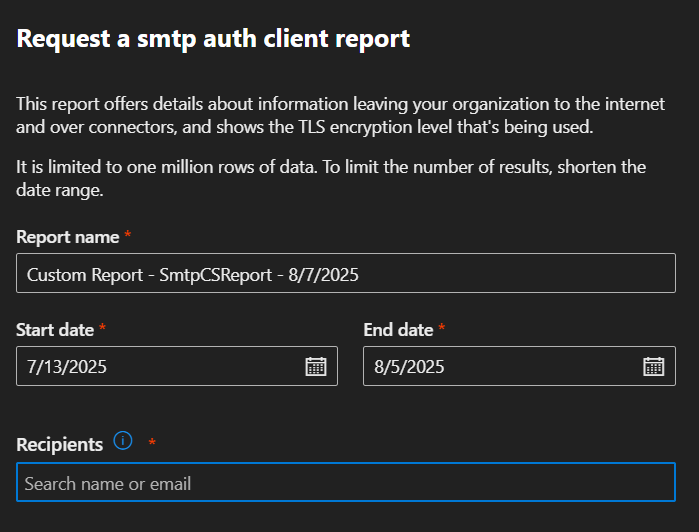
You’ll receive a download link at the address specified.
Get detailled SMTP Auth Report via PowerShell
If you follow this blog or my posts on LinkedIn, you know I’m not a fan of too much "click-click", I prefer going straight to the point (via PowerShell or other tools).
As previously mentioned, you can request a report from the report page. But if you prefer to do it directly via PowerShell, it’s possible:
Start-HistoricalSearch -ReportTitle "Custom SMTPBasicAuth" -ReportType "SmtpCSReport" -StartDate (Get-Date).AddDays(-2) -EndDate (Get-Date) -NotifyAddress [email protected]To check the progress status:
Get-HistoricalSearch | Select-Object Identity, SubmitDate, Status, ReportTitle, EstimatedCompletionTime, JobProgress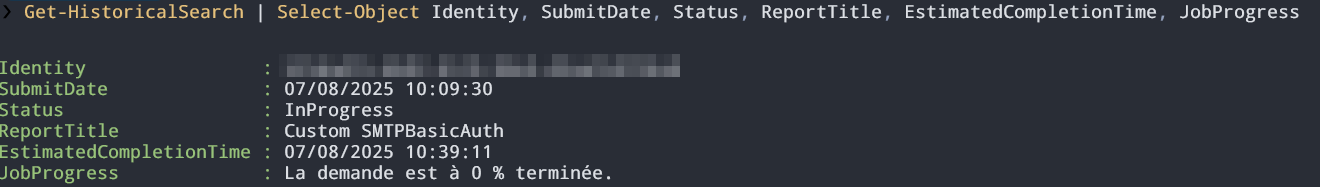
You’ll receive a download link at the address specified in NotifyAddress. Depending on your email volume, report generation may take several hours.
Early end of SMTP Basic Auth
My tenant is already blocked for sending via SMTP Basic Auth
If you have never used Basic Authentication, it is likely that Microsoft has already disabled SMTP Basic Auth. In fact, in their article about the end of Basic Auth on other protocols at the end of 2022:
What we are changing
We removed the ability to use Basic authentication in Exchange Online for Exchange ActiveSync (EAS), POP, IMAP, Remote PowerShell, Exchange Web Services (EWS), Offline Address Book (OAB), Autodiscover, Outlook for Windows, and Outlook for Mac.
We also disabled SMTP AUTH in all tenants where it wasn't being used.
You can check this with the command :
Get-TransportConfig | Select SmtpClientAuthenticationDisabledIf it's True, then it's already disabled on your tenant.
Although I don't recommend reactivating it, you can reactivate it using :
Set-TransportConfig -SmtpClientAuthenticationDisabled $falseI want to disable SMTP Basic Auth globally now
If you don't want to wait for Microsoft to disable it, you can disable SMTP Basic Auth for your entire organization right now:
Set-TransportConfig | Select SmtpClientAuthenticationDisabledI want to disable SMTP Basic Auth on only a few mailboxes right now
You can also block SMTP Basic Auth on most of your mailboxes, while retaining a few for the time it takes to migrate them. To block SMTP Basic Auth on a box :
Set-CASMailbox -Identity <MailboxIdentity> -SmtpClientAuthenticationDisabled $falseReplacement Solutions for SMTP Auth
You have several options:
- Third-party solution: I recommend Postmark, which I’ve used for years:
- No SPF modification needed (a big plus in some cases)
- Template management
- Access via API and classic SMTP
- Sending from a specific address or domain
Perfect for applications, developers, and automation platforms (available modules in Make, n8n, and Zapier)
- Azure ACS
- Microsoft High Volume EMAIL (HVE):
- Still in Public Preview.
- HVE supports only the sending of e-mails to internal recipients (=within the tenant). The possibility of sending e-mails to external recipients was removed in June 2025.
- The account must be excluded from conditional access policies, especially MFA. A dedicated article will be published soon.
- SMTP relay with connector in Exchange Online
- Exchange Online account with SMTP OAuth
- Any other e-mail solution (Postfix, etc.).
General recommendations regardless of your choice:
- uses a currently supported solution to avoid having to start all over again in a few months' time. That's why I haven't included IIS SMTP (which is based on IIS 6, unsupported for many, many years and even discontinued as of Windows Server 2025), nor hMail, which have been widely used solutions but are no longer supported.
- do not use Exchange Online’s Direct Send as a replacement (anonymous sending without a connector), it’s even recommended to block it: https://itpro-tips.com/block-direct-send-in-exchange-online/
- secure your sending platform: unauthorized access can be a serious risk, especially if you handle client domains (marketing, mass mailing, etc.)
- use a dedicated subdomain like
app.domain.comfor application messaging.
![End of Basic Authentication for SMTP in Exchange Online: new dates, report, and PowerShell [February 2026 update]](https://images.unsplash.com/photo-1522096823084-2d1aa8411c13?crop=entropy&cs=tinysrgb&fit=max&fm=jpg&ixid=M3wxMTc3M3wwfDF8c2VhcmNofDF8fHNlbmR8ZW58MHx8fHwxNzU0NTYxOTI4fDA&ixlib=rb-4.1.0&q=80&w=1024)


Comments