The Microsoft Store can pose a significant risk to admins who use it to deploy apps through Intune. While the Store was created to be a convenient hub for users to manage their applications, the reality is that many apps on the store are not published by the actual developers of the software.
Instead, they are published by third-party individuals who may not be affiliated with the original creators. This poses a serious security problem, as these unofficial packages may not receive updates or could potentially contain spyware or malware.
In contrast, applications sourced from winget are published by the developers themselves and are much safer. For example, popular apps like Notepad++ or 7-zip are either non-existent on the Microsoft Store or are riddled with unofficial, sketchy 3rd party publishers.
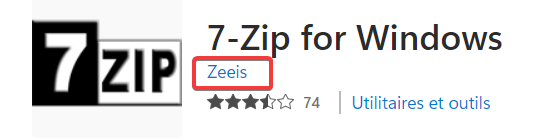
Let's take an example with 7zip. Although a 7-Zip for Windows is available in the Microsoft Store for Windows, it is worth noting that the software's developer, Igor Pavlov, is not the publisher of the app. Instead, it is published by an anonymous user called Zeeis. So I would not recommend deploying this app...
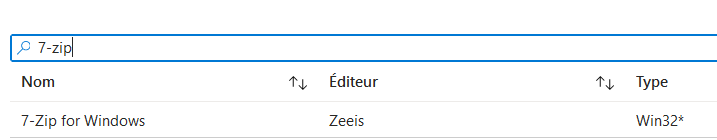
When we look for 7-zip in Intune, we can find it too.
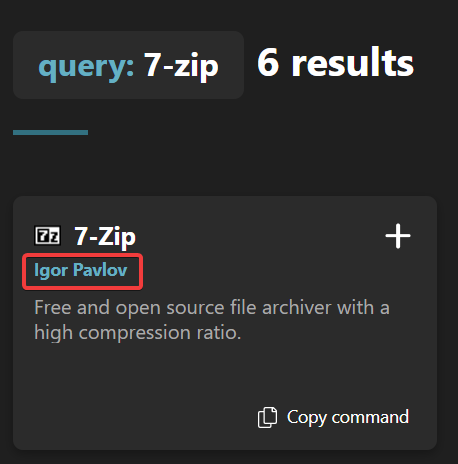
In we look for 7-zip in winget repo, we get the real application developed and published by Igor Pavlov:
The danger lies in the ease of access and convenience of the Microsoft Store. It's easy for an administrator to push out these unofficial packages through Intune, thinking they are safe and legitimate, only to be left with a package that eventually becomes outdated or, worse, infected with malware.
It's important for admins to be aware of the risks associated with the Microsoft Store and to do their research before deploying any apps. With the rise of remote work and the need for efficient app management, it's essential to prioritize security and only deploy applications from reputable sources (winget for example).



Comments