When it comes to enabling Single Sign-On (SSO) on Windows devices, understanding the differences between Primary Refresh Token (PRT) and Seamless SSO (Microsoft Entra Seamless Single Sign-On) is crucial. Both approaches have their strengths and are tailored to specific scenarios. Here’s what IT Pros need to know.
Seamless SSO: the legacy option
Seamless SSO is designed for older operating systems such as Windows 7 and Windows 8.1. It provides an effortless sign-on experience for users in environments where devices are:
- Domain-Joined: Seamless SSO requires devices to be connected to an Active Directory domain.
Limitations
- Seamless SSO is not used on Windows 10/11 devices that are Microsoft Entra Joined or Hybrid Joined.
Seamless SSO needs the user's device to be domain-joined, but it isn't used on Windows 10 [and 11] Microsoft Entra joined devices or Microsoft Entra hybrid joined devices.
source : https://learn.microsoft.com/en-us/entra/identity/hybrid/connect/how-to-connect-sso#sso-via-primary-refresh-token-vs-seamless-sso
When reading this, you might think, "This might be useless in my environment," .and well... yes!😄
- Seamless SSO also requires the password of the
AZUREADSSOACCaccount to be periodically renewed, adding an extra layer of management and a potential security risk. By moving away from Seamless SSO, you eliminate this concern and simplify security management. - Requires browser configuration, notably through registry keys and/or GPOs for the
autologon.microsoftazuread-sso.comregistration, which complicates implementation (https://learn.microsoft.com/en-us/entra/identity/hybrid/connect/how-to-connect-sso-quick-start).
Non-functionality and security risks
Based on my experience with dozens of clients over the years, browser configuration via GPO or registry keys is often missing, or users rely on a browser that does not support it.
Thus, even if you intended to leverage Seamless SSO (outside of Entra ID joined/hybrid PCs), it is likely that the configuration was never completed, rendering the feature useless.
Furthermore, keeping this option enabled exposes you to potential exploitation by attackers, as highlighted in these articles:
- Advanced Active Directory to Entra ID lateral movement techniques (Blackhat August 2025) by Dirk-jan Mollema
- Impersonating Office 365 Users With Mimikatz by Michael Grafnetter
Primary Refresh Token (PRT): the go-to for modern windows systems
For Windows 10, Windows Server 2016, and later versions, SSO via Primary Refresh Token (PRT) is the recommended solution. PRT works seamlessly on devices registered with Microsoft Entra ID. This includes:
- Microsoft Entra Hybrid Joined Devices: Domain-joined devices synced to Microsoft Entra ID.
- Microsoft Entra Joined Devices: Devices directly registered with Microsoft Entra ID.
- Personal Registered Devices: Configured through the "Add Work or School Account" feature.
Key Benefits of PRT-Based SSO
- Modern Authentication: PRT leverages token-based authentication, reducing reliance on legacy protocols.
- Broad Compatibility: Works across hybrid and cloud-only environments.
- Enhanced Security: Supports features like Conditional Access and Multifactor Authentication.
For detailed guidance, refer to Microsoft’s documentation: https://learn.microsoft.com/en-us/azure/active-directory/devices/concept-primary-refresh-token.
Audit the use of Seamless SSO
On the Entra ID side, there doesn't seem to be any logs related to Seamless SSO (to be confirmed).
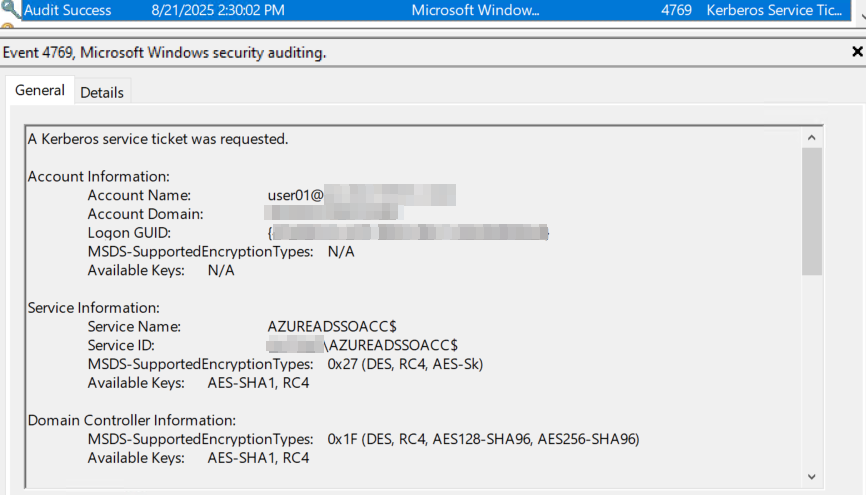
However, on the AD side, we can analyze the 4769 events across all domain controllers, targeting those where the Service Name equals AZUREADSSOACC$.
We get the name of the user who logged in from Account name (this may vary depending on the OS language).
Or with PowerShell :
Get-WinEvent -FilterHashtable @{LogName='Security'; ID=4769} | Where-Object {$_.Message -like "*azureadssoacc$*"}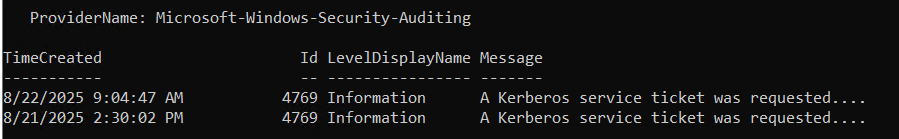
If you just want to retrieve the user names and the date:
Get-WinEvent -FilterHashtable @{LogName='Security'; ID=4769} |
Where-Object {$_.Message -like "*azureadssoacc$*"} |
ForEach-Object {
$lines = $_.Message -split "`r?`n"
# The 4th line (index 3) contains "Account Name: xxxx"
if ($lines.Count -ge 4) {
$accountLine = $lines[3]
# Extract what follows "Account Name:" removing tabs/spaces
if ($accountLine -match ":\s*(.+)$") {
[PSCustomObject]@{
TimeCreated = $_.TimeCreated
AccountName = $matches[1].Trim()
}
}
}
}How to Remove Seamless SSO
To completely remove Seamless SSO from your environment, follow these steps:
- Disable the Seamless SSO feature in Microsoft Entra Connect Sync (formerly known as Azure AD Connect).
- Remove the
AZUREADSSOACCobject from Active Directory. - Delete the registry keys related to the Seamless SSO configuration for browsers.
These actions ensure a clean removal of the feature, reducing legacy dependencies and potential security risks. For any additional guidance or support, feel free to contact me.



Comments